New analysis has uncovered safety vulnerabilities in a number of tunneling protocols that might enable attackers to carry out a variety of assaults.
“Web hosts that settle for tunneling packets with out verifying the sender’s identification might be hijacked to carry out nameless assaults and supply entry to their networks,” Top10VPN stated in a examine, as a part of a collaboration with KU Leuven professor and researcher Mathy Vanhoef.
As many as 4.2 million hosts have been discovered vulnerable to the assaults, together with VPN servers, ISP house routers, core web routers, cell community gateways, and content material supply community (CDN) nodes. China, France, Japan, the U.S., and Brazil high the record of probably the most affected international locations.
Profitable exploitation of the shortcomings may allow an adversary to abuse a vulnerable system as one-way proxies, in addition to conduct denial-of-service (DoS) assaults.
“An adversary can abuse these safety vulnerabilities to create one-way proxies and spoof supply IPv4/6 addresses,” the CERT Coordination Middle (CERT/CC) stated in an advisory. “Weak programs can also enable entry to a corporation’s non-public community or be abused to carry out DDoS assaults.”
The vulnerabilities are rooted in the truth that the tunneling protocols akin to IP6IP6, GRE6, 4in6, and 6in4, that are primarily used to facilitate information transfers between two disconnected networks, don’t authenticate and encrypt site visitors with out satisfactory safety protocols like Web Protocol Safety (IPsec).
The absence of further safety guardrails opens the door to a state of affairs the place an attacker can inject malicious site visitors right into a tunnel, a variation of a flaw that was beforehand flagged in 2020 (CVE-2020-10136).
They’ve been assigned the next CVE identifiers for the protocols in query –
- CVE-2024-7595 (GRE and GRE6)
- CVE-2024-7596 (Generic UDP Encapsulation)
- CVE-2025-23018 (IPv4-in-IPv6 and IPv6-in-IPv6)
- CVE-2025-23019 (IPv6-in-IPv4)
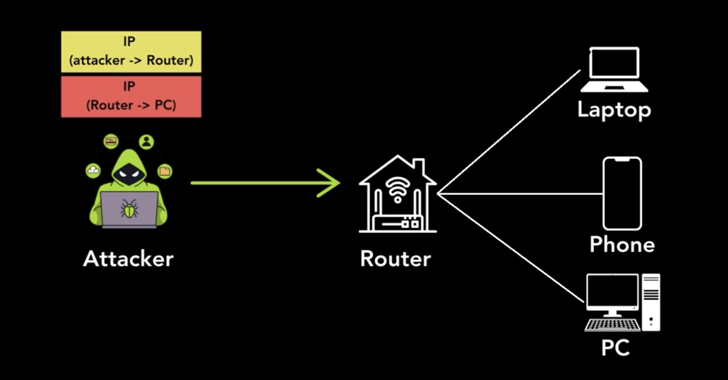
“An attacker merely must ship a packet encapsulated utilizing one of many affected protocols with two IP headers,” Top10VPN’s Simon Migliano defined.
“The outer header comprises the attacker’s supply IP with the susceptible host’s IP because the vacation spot. The internal header’s supply IP is that of the susceptible host IP reasonably than the attacker. The vacation spot IP is that of the goal of the nameless assault.”
Thus when the susceptible host receives the malicious packet, it mechanically strips the outer IP handle header and forwards the internal packet to its vacation spot. Provided that the supply IP handle on the internal packet is that of the susceptible however trusted host, it is in a position to get previous community filters.
As defenses, it is advisable to make use of IPSec or WireGuard to offer authentication and encryption, and solely settle for tunneling packets from trusted sources. On the community degree, it is also suggested to implement site visitors filtering on routers and middleboxes, perform Deep packet inspection (DPI), and block all unencrypted tunneling packets.
“The influence on victims of those DoS assaults can embrace community congestion, service disruption as assets are consumed by the site visitors overload, and crashing of overloaded community units,” Migliano stated. “It additionally opens up alternatives for additional exploitation, akin to man-in-the-middle assaults and information interception.”