Cybersecurity researchers have warned of a brand new large-scale marketing campaign that exploits safety flaws in AVTECH IP cameras and Huawei HG532 routers to rope the units right into a Mirai botnet variant dubbed Murdoc_Botnet.
The continued exercise “demonstrates enhanced capabilities, exploiting vulnerabilities to compromise units and set up expansive botnet networks,” Qualys safety researcher Shilpesh Trivedi stated in an evaluation.
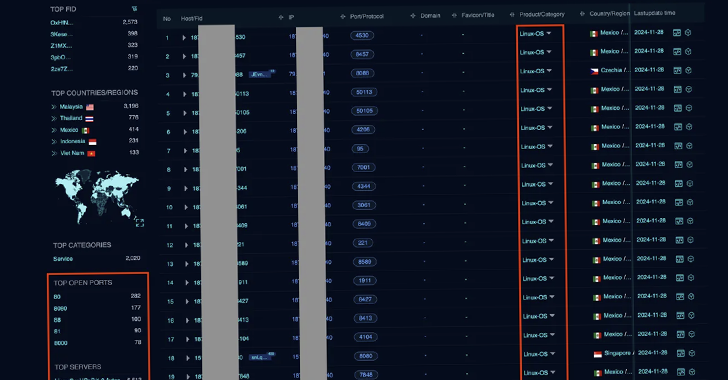
The marketing campaign is understood to be lively since a minimum of July 2024, with over 1,370 methods contaminated so far. A majority of the infections have been situated in Malaysia, Mexico, Thailand, Indonesia, and Vietnam.
Proof exhibits that the botnet leverages recognized safety flaws reminiscent of CVE-2017-17215 and CVE-2024-7029 to realize preliminary entry to the Web of Issues (IoT) units and obtain the subsequent stage payload via a shell script.
The script, for its half, fetches the botnet malware and executes it relying on the CPU structure. The tip objective of those assaults is to weaponize the botnet for finishing up distributed denial-of-service (DDoS) assaults.
The event comes weeks after a Mirai botnet variant named gayfemboy was discovered exploiting a not too long ago disclosed safety flaw impacting 4-Religion industrial routers since early November 2024. Again in mid-2024, Akamai additionally revealed that CVE-2024-7029 was abused by malicious actors to enlist AVTECH units right into a botnet.

Final week, particulars emerged about one other large-scale DDoS assault marketing campaign concentrating on main Japanese firms and banks because the finish of 2024 by making use of an IoT botnet shaped by exploiting vulnerabilities and weak credentials. A number of the different targets are concentrated across the U.S., Bahrain, Poland, Spain, Israel, and Russia.
The DDoS exercise has been discovered to single out telecommunications, know-how, internet hosting, cloud computing, banking, gaming, and monetary companies sectors. Over 55% of the compromised units are situated in India, adopted by South Africa, Brazil, Bangladesh, and Kenya.
“The botnet contains malware variants derived from Mirai and BASHLITE,” Pattern Micro stated. “The botnet’s instructions embrace these that may incorporate numerous DDoS assault strategies, replace malware, and allow proxy companies.”
The assaults contain infiltrating IoT units to deploy a loader malware that fetches the precise payload, which then connects to a command-and-control (C2) server and awaits additional directions for DDoS assaults and different functions.
To safeguard in opposition to such assaults, it is suggested to observe suspicious processes, occasions, and community visitors spawned by the execution of any untrusted binary/scripts. It is also advisable to use firmware updates and alter the default username and password.