The Iranian nation-state actor often called MuddyWater has been noticed utilizing a never-before-seen backdoor as a part of a current assault marketing campaign, shifting away from its well-known tactic of deploying authentic distant monitoring and administration (RMM) software program for sustaining persistent entry.
That is in accordance with impartial findings from cybersecurity corporations Test Level and Sekoia, which have codenamed the malware pressure BugSleep and MuddyRot, respectively.
“In comparison with earlier campaigns, this time MuddyWater modified their an infection chain and didn’t depend on the authentic Atera distant monitoring and administration software (RRM) as a validator,” Sekoia mentioned in a report shared with The Hacker Information. “As an alternative, we noticed that they used a brand new and undocumented implant.”
Some parts of the marketing campaign had been first shared by Israeli cybersecurity firm ClearSky on June 9, 2024. Targets embody nations like Turkey, Azerbaijan, Jordan, Saudi Arabia, Israel, and Portugal.
MuddyWater (aka Boggy Serpens, Mango Sandstorm, and TA450) is a state-sponsored risk actor that is assessed to be affiliated with Iran’s Ministry of Intelligence and Safety (MOIS).
Cyber assaults mounted by the group have been pretty constant, leveraging spear-phishing lures in e-mail messages to ship varied RMM instruments like Atera Agent, RemoteUtilities, ScreenConnect, SimpleHelp, and Syncro.
Earlier this April, HarfangLab mentioned it observed an uptick in MuddyWater campaigns delivering Atera Agent since late October 2023 to companies throughout Israel, India, Algeria, Turkey, Italy, and Egypt. The sectors focused embody airways, IT corporations, telecoms, pharma, automotive manufacturing, logistics, journey, and tourism.
“MuddyWater locations a excessive precedence on getting access to enterprise e-mail accounts as a part of their ongoing assault campaigns,” the French cybersecurity agency famous on the time.

“These compromised accounts function invaluable assets, enabling the group to boost the credibility and effectiveness of their spear-phishing efforts, set up persistence inside focused organizations, and evade detection by mixing in with authentic community visitors.”
The most recent assault chains are not any completely different in that compromised e-mail accounts belonging to authentic corporations are used to ship spear-phishing messages that both include a direct hyperlink or a PDF attachment pointing to an Egnyte subdomain, which has been beforehand abused by the risk actor to propagate Atera Agent.
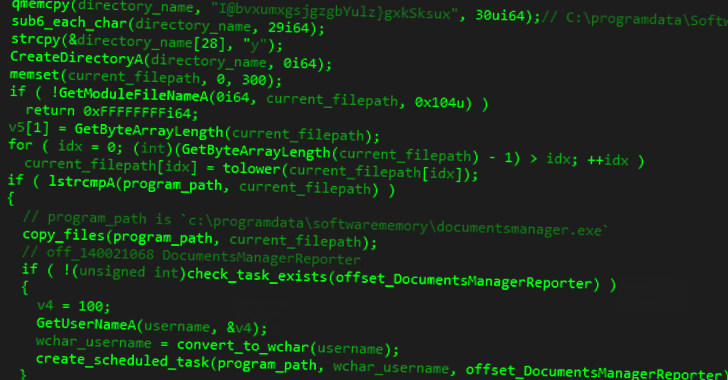
BugSleep, aka MuddyRot, is an x64 implant developed in C that comes outfitted with capabilities to obtain/add arbitrary information to/from the compromised host, launch a reverse shell, and arrange persistence. Communications with a command-and-control (C2) server happen over a uncooked TCP socket on port 443.
“The primary message to be despatched to the C2 is the sufferer host fingerprint, which is the mix of the hostname and the username joined by a slash,” Sekoia mentioned. “If the sufferer obtained ‘-1,’ this system stops, in any other case the malware enters in an infinite loop to await new order from the C2.”
It is at present not clear why MuddyWater has switched to utilizing a bespoke implant, though it is suspected that the elevated monitoring of RMM instruments by safety distributors could have performed a component.
“The elevated exercise of MuddyWater within the Center East, notably in Israel, highlights the persistent nature of those risk actors, who proceed to function in opposition to all kinds of targets within the area,” Test Level mentioned.
“Their constant use of phishing campaigns, now incorporating a customized backdoor, BugSleep, marks a notable improvement of their strategies, techniques, and procedures (TTPs).”