Customers of Cleo-managed file switch software program are being urged to make sure that their cases aren’t uncovered to the web following stories of mass exploitation of a vulnerability affecting absolutely patched techniques.
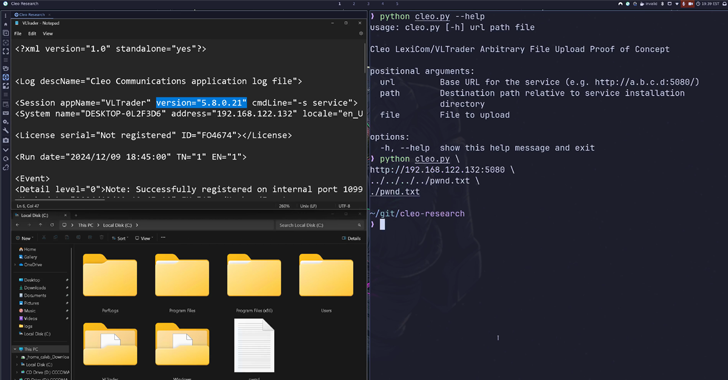
Cybersecurity firm Huntress mentioned it found proof of menace actors exploiting the problem en masse on December 3, 2024. The vulnerability, which impacts Cleo’s LexiCom, VLTransfer, and Concord software program, issues a case of unauthenticated distant code execution.
The safety gap is tracked as CVE-2024-50623, with Cleo noting that the flaw is the results of an unrestricted file add that might pave the best way for the execution of arbitrary code.
The Illinois-based firm, which has over 4,200 prospects internationally, has since issued one other advisory (CVE pending), warning of a separate “unauthenticated malicious hosts vulnerability that might result in distant code execution.”
The event comes after Huntress mentioned the patches launched for CVE-2024-50623 don’t fully mitigate the underlying software program flaw. The difficulty impacts the beneath merchandise and is predicted to be patched later this week –
- Cleo Concord (as much as model 5.8.0.23)
- Cleo VLTrader (as much as model 5.8.0.23)
- Cleo LexiCom (as much as model 5.8.0.23)
Within the assaults detected by the cybersecurity firm, the vulnerability has been discovered to be exploited to drop a number of information, together with an XML file that is configured to run an embedded PowerShell command that is chargeable for retrieving a next-stage Java Archive (JAR) file from a distant server.
Particularly, the intrusions leverage the very fact information positioned within the “autorun” sub-directory throughout the set up folder and are instantly learn, interpreted, and evaluated by the vulnerable software program.
As many as not less than 10 companies have had their Cleo servers compromised, with a spike in exploitation noticed on December 8, 2024, at round 7 a.m. UTC. Proof gathered to date pins the earliest date of exploration to December 3, 2024.
Sufferer organizations span shopper product firms, logistics and delivery organizations, and meals suppliers. Customers are suggested to make sure that their software program is up-to-date to make sure that they’re protected in opposition to the menace.
Ransomware teams like Cl0p (aka Lace Tempest) have beforehand set their sights on numerous managed file switch instruments previously, and it appears like the most recent assault exercise isn’t any completely different.
In keeping with safety researcher Kevin Beaumont (aka GossiTheDog), “Termite ransomware group operators (and possibly different teams) have a zero-day exploit for Cleo LexiCom, VLTransfer, and Concord.”
Cybersecurity firm Rapid7 mentioned it additionally has confirmed profitable exploitation of the Cleo challenge in opposition to buyer environments. It is price noting that Termite has claimed duty for the current cyber assault on provide chain agency Blue Yonder.
Broadcom’s Symantec Risk Hunter Workforce instructed The Hacker Information that “Termite seems to be utilizing a modified model of Babuk ransomware, which, when executed on a machine, encrypts focused information and provides a .termite extension.”
“Since we noticed that Blue Yonder had an occasion of Cleo’s software program open to the web by way of Shodan, and Termite has claimed Blue Yonder amongst its victims, which was additionally confirmed by their itemizing and open listing of information, I would say that Gossi is right in his assertion,” Jamie Levy, Huntress’ Director of Adversary Techniques, instructed the publication.
“For what it is price, there have been some rumblings that Termite is likely to be the brand new Cl0p, there may be some information that appears to help this as Cl0p’s actions have waned whereas Termite’s actions have elevated. They’re additionally working in some related fashions. We’re not likely within the attribution recreation, but it surely would not be stunning in any respect if we’re seeing a shift in these ransomware gangs for the time being.”
(This can be a growing story. Please examine again for extra updates.)