The China-linked risk actor generally known as MirrorFace has been attributed to a brand new spear-phishing marketing campaign primarily focusing on people and organizations in Japan since June 2024.
The goal of the marketing campaign is to ship backdoors generally known as NOOPDOOR (aka HiddenFace) and ANEL (aka UPPERCUT), Development Micro mentioned in a technical evaluation.
“An fascinating facet of this marketing campaign is the comeback of a backdoor dubbed ANEL, which was utilized in campaigns focusing on Japan by APT10 till round 2018 and had not been noticed since then,” safety researcher Hara Hiroaki mentioned.
It is price noting that MirrorFace’s use of ANEL was additionally documented by ESET final month as a part of a cyber assault focusing on a diplomatic group within the European Union utilizing lures associated to the World Expo.
MirrorFace, also referred to as Earth Kasha, is the identify given to a Chinese language risk actor that is recognized for its persistent focusing on of Japanese entities. It is assessed to be a sub-cluster inside APT10.
The most recent marketing campaign is a departure from the hacking group’s intrusions noticed throughout 2023, which primarily sought to use safety flaws in edge gadgets from Array Networks and Fortinet for preliminary entry.
The swap to spear-phishing e-mail messages is intentional, per Development Micro, and a call motivated by the truth that the assaults are designed to single out people reasonably than enterprises.
“Moreover, an evaluation of the sufferer profiles and the names of the distributed lure information means that the adversaries are significantly interested by matters associated to Japan’s nationwide safety and worldwide relations,” Hiroaki identified.

The digital missives, despatched from both free e-mail accounts or compromised accounts, include a hyperlink to Microsoft OneDrive. They goal to lure recipients into downloading a booby-trapped ZIP archive utilizing themes associated to interview requests and Japan’s financial safety from the attitude of present U.S.-China relations.
Development Micro mentioned the contents of the ZIP archive differ relying on the targets, including it uncovered three totally different an infection vectors which were used to ship a malicious dropper dubbed ROAMINGMOUSE –
- A macro-enabled Phrase doc
- A Home windows shortcut file that executes a self-extracting archive (SFX), which then masses a macro-enabled template doc
- A Home windows shortcut file that executes PowerShell accountable for dropping an embedded cupboard archive, which then masses a macro-enabled template doc
The macro-enabled doc, ROAMINGMOUSE, acts as a dropper for elements associated to ANEL and finally launches the backdoor, whereas concurrently incorporating evasion methods that conceal it from safety applications and make detection difficult.
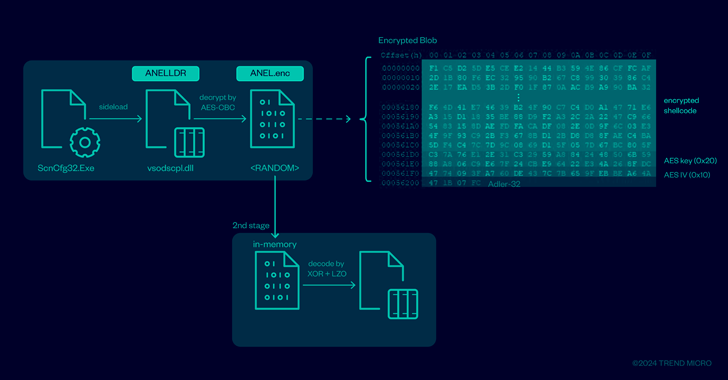
One of many modules deployed by way of the dropper is ANELLDR, a loader that is designed to execute ANEL in reminiscence. It is launched utilizing a recognized technique known as DLL side-loading, after which it decrypts and runs the final-stage backdoor.
A 32-bit HTTP-based implant, ANEL was actively developed between 2017 and 2018 as a method to seize screenshots, add/obtain information, load executables, and run instructions by way of cmd.exe. The 2024 marketing campaign employs an up to date model that introduces a brand new command to run a specified program with elevated privileges.
Moreover, the assault chains leverage the backdoor to gather info from the contaminated environments and selectively deploy NOOPDOOR towards targets of particular curiosity.
“Most of the targets are people, similar to researchers, who could have totally different ranges of safety measures in place in comparison with enterprise organizations, making these assaults harder to detect,” Hiroaki mentioned. “It’s important to keep up fundamental countermeasures, similar to avoiding opening information hooked up to suspicious emails.”