Attackers are actually focusing on a important authentication bypass vulnerability within the CrushFTP file switch software program utilizing exploits based mostly on publicly out there proof-of-concept code.
The safety vulnerability (CVE-2025-2825) was reported by Outpost24, and it permits distant attackers to achieve unauthenticated entry to gadgets working unpatched CrushFTP v10 or v11 software program.
“Please take fast motion to patch ASAP. The underside line of this vulnerability is that an uncovered HTTP(S) port might result in unauthenticated entry,” CrushFTP warned in an e mail despatched to clients on Friday, March 21, when it launched patches to deal with the safety flaw.
As a workaround, admins who cannot instantly replace CrushFTP 10.8.4 and later or 11.3.1 and later can allow the DMZ (demilitarized zone) perimeter community choice to guard their CrushFTP servers till they’ll patch.
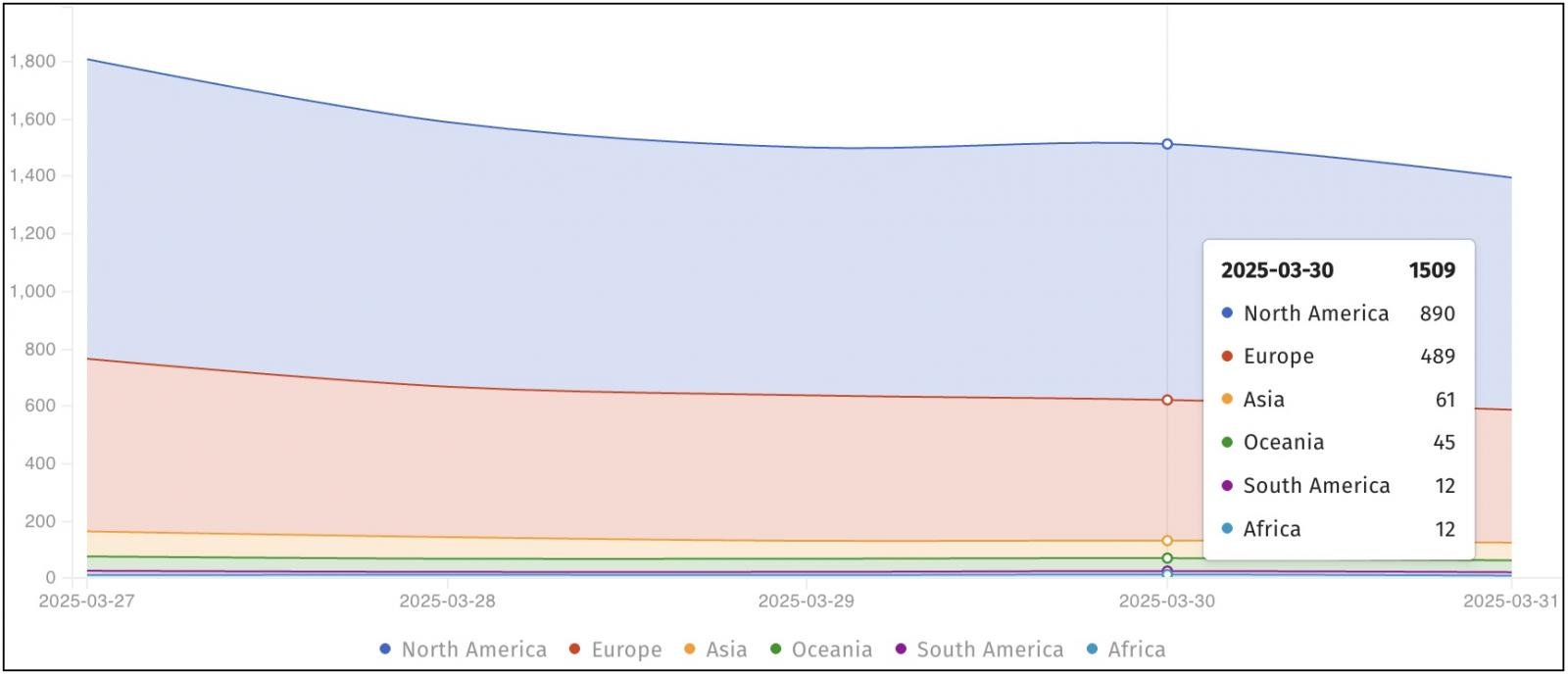
Every week later, safety menace monitoring platform Shadowserver warned that its honeypots detected dozens of exploitation makes an attempt focusing on Web-exposed CrushFTP servers, with over 1,500 susceptible situations uncovered on-line.
The warning comes days after ProjectDiscovery printed a write-up containing CVE-2025-2825 technical particulars and a proof-of-concept exploit.
“We’re observing CrushFTP CVE-2025-2825 exploitation makes an attempt based mostly on publicly out there PoC exploit code,” Shadowserver mentioned on Monday. “Nonetheless 1512 unpatched situations susceptible to CVE-2025-2825 seen on 2025-03-30.”
File switch merchandise akin to CrushFTP are excessive on ransomware gangs’ checklist of targets, particularly Clop, which has been linked to information theft assaults focusing on zero-day flaws in Accelion FTA, MOVEit Switch, GoAnywhere MFT, and, most just lately, Cleo software program.
One yr in the past, in April 2024, CrushFTP patched an actively exploited zero-day vulnerability (tracked as CVE-2024-4040) that allow unauthenticated attackers escape the person’s digital file system (VFS) and obtain system information.
On the time, cybersecurity firm CrowdStrike discovered proof that the marketing campaign focusing on CrushFTP servers at a number of U.S. organizations was seemingly politically motivated and targeted on intelligence-gathering.
The Cybersecurity and Infrastructure Safety Company (CISA) additionally added CVE-2024-4040 to its Recognized Exploited Vulnerabilities catalog, ordering federal businesses to safe susceptible methods on their networks inside every week.
CrushFTP clients had been additionally warned to patch a important distant code execution bug (CVE-2023-43177) within the firm’s enterprise suite in November 2023 after Converge safety researchers (who found and reported the flaw) launched a proof-of-concept exploit three months after safety updates had been launched.

Based mostly on an evaluation of 14M malicious actions, uncover the highest 10 MITRE ATT&CK strategies behind 93% of assaults and learn how to defend towards them.








